 Critical Memova-based webmail vulnerability put at risk more than 40 million webmail accounts Critical Memova-based webmail vulnerability put at risk more than 40 million webmail accounts
Written by DPSunday, 29 March 2009Independent security researchers Rosario Valotta and Matteo Carli have discovered a critical security vulnerability impacting all worldwide webmail applications based on the Memova framework (developed by Critical Path); among these:
- Tiscali IT/UK/NL
- Wind
- Telecom
- Vodafone
- Swisscom
- Telefonica
- Virgin
- Sonera
- Terra.es
- Telia
- T-Mobile
- Fastweb
By exploiting this security flaw, an attacker can stealthly tamper a victim's webmail settings, thus allowing incoming e-mails to be automatically forwarded to his inbox.
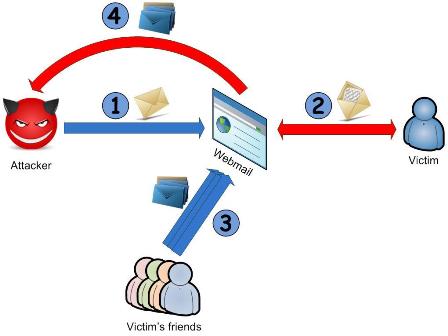
In this way, the attacker can read the e-mail messages of millions of customers by simply checking his webmail account.
The attack is based upon two different vulnerabilities, found on the analyzed webmails:
• Cross site scripting – XSS
• Cross site request forgery – CSRF
There were more than *40 million mail accounts* worldwide exposed to this critical threat.
For detailed information and PoC, read the advisory (Italian).
The bug has been reported to Critical path and they fixed it in few days.
A video demonstration is available at:
http://www.matteocarli.com/files/2009/03/fwd2_press.swf
Thanks to Rosario and Matteo for their report.
| 